E-Mail Phishing
Recently members of one of my mailing lists received e-mail purportedly from me, and thought that I had been hacked. I am quite paranoid about computer security, so know that my systems are all secure. It takes several hours a week (at least) to do this. What I believe happened is that someone on my list has been hacked, and one of my e-mail messages to the list was intercepted, and the list was used for phishing purposes.
We all need to know how to identify perhaps innocent-looking e-mails that are maliciously directed at us. I really recommend using Google's Gmail because it is very effective at filtering out such messages. Here is an example of a phishing message from my gmail spam folder: (I have highlighted suspicious things for your edification, but the whole message reeks of unreality.)
Bank of America
115 W 42nd St, New York, NY 10036, USA
From Desktop of Mr. Jeff Anderson
Our Ref: BOF-0XX2/987/20
E-mail: jeff44105@gmail.com
It is my modest obligation to write you this letter as regards the Authorization of your owed payment through our most respected financial institution (Bank of America). I am Mr. Jeff Anderson, TRANSFER INSPECTION OFFICER, foreign operations Department Bank of America, the British Government in Conjunction with us government, World Bank, united Nations Organization on foreign Payment matters has empowered my bank after much consultation and consideration to handle all foreign payments and release them to their appropriate beneficiaries with the help of a Representative from Federal Reserve Bank of New York.
As the newly Appointed/Accredited International Paying Bank, We have been instructed by the world governing body together with the committee on international debt reconciliation department to release your overdue funds with immediate effect; with this exclusive vide transaction no.: wha/eur/202,password: 339331, pin code: 78569, having received these vital payment numbers, you are instantly qualified to receive and confirm your payment with us within the next 96hrs.
Be informed that we have verified your payment file as directed to us and your name is next on the list of our outstanding fund beneficiaries to receive their payment. Be advised that because of too many funds beneficiaries, you are entitled to receive the sum of $14.5M,(Fourteen Million Five Hundred Thousand Dollars only), as to enable us pay other eligible beneficiaries.
To facilitate with the process of this transaction, please kindly re-confirm the following information below:
1) Your Full Name:
2) Your Full Address:
3) Your Contact Telephone and Fax No:
4) Your Profession, Age and Marital Status:
5) Any Valid Form of Your Identification/Driver's License:
6) Bank Name:
7) Bank Address:
8) Account Name:
9) Account Number:
10) Swift Code:
11) Routing Number:
As soon as we receive the above mentioned information, your payment will be processed and released to you without any further delay. This notification email should be your confidential property to avoid impersonators claiming your fund. You are required to provide the above information for your transfer to take place through Bank to Bank Transfer directly from Bank of America
We Look Forward To Serving You Better.
Mr. Jeff Anderson,
TRANSFER INSPECTION OFFICER
Bank of America
The information they request is sufficient for the sender to clean out your banking account!
Note that it is trivially easy to change the From: name of the message sender, so you can never trust this. But you can go further to see who really sent this; in Thunderbird, you can do this in the View menu and selecting headers/all. Or, you can use View/Message Source. You will then be presented with the full route that the e-mail took through the internet:
Delivered-To: jamesrome@gmail.com
Received: by 2002:a67:dd83:0:0:0:0:0 with SMTP id i3-v6csp981460vsk;
Sat, 1 Sep 2018 16:10:47 -0700 (PDT)
X-Google-Smtp-Source: ANB0VdZP5hl5aj9eEycLEMUKsu50rwHbVtD3eFwrpKkxQHSyScHj/buTJ31eUH8T0iuli8JSma2P
X-Received: by 2002:a63:24c:: with SMTP id 73-v6mr20914277pgc.252.1535843447249;
Sat, 01 Sep 2018 16:10:47 -0700 (PDT)
ARC-Seal: i=1; a=rsa-sha256; t=1535843447; cv=none;
d=google.com; s=arc-20160816;
b=KAmB+sKtR/d9gocNxjvx98I1V9pudt4YlnOs5PTSuzBLVccJkrQTh+n7MzxwD4RIeW
SaYxDe3AzP8vaC28gVlhItq8Ao4sgVbTsnkf2OAraAm77V+dMUXcQaxu4xqGM57p8e68
Yv1ofDOIM3PxtsmiqlV6BE2qXoqlhazHzI4uEx72snRuTw91IIeHo3xCid3c0A0q3J+4
Ty6CCKRvEF1PPy0F5NQazmhW+CDhMx/+ARpBZpDgZyV6YgTyoXbVLJGYFIKm+DKKgRuG
sVSO6tNvo2wLqpqu9MSk3N1FJ4mRid1cJfId36+5Kt1Nq/9CRWAW3yIMivYE8MuA/UVN
LhDA==
ARC-Message-Signature: i=1; a=rsa-sha256; c=relaxed/relaxed; d=google.com; s=arc-20160816;
h=to:message-id:content-transfer-encoding:mime-version:date:subject
:from:reply-to:arc-authentication-results;
bh=+qiV0KE8J5jwioiXhBhoxbc+f5PGBxBFMIyJrH38oCI=;
b=Lnqr7bTEoytKYtdNGUKvzaWrWyp5LWeiykKI8vZBCFRpVELXXQnFve7dbX9RzKrjjr
ZJpTNjhF0VG5Q2yIsymAAFGt57UYtM5OqZuLACR0VgL3OWbhgHPwF3lyQ926XFKDGPe/
7IXq2itfDJcee2EvdERgoSyIrgRqmg3Q18aQzcsm8FLdFADFwS3oIhDKEQFGTpGye3PQ
B46nmGwWMIdhNLeycSyr37519/dfXK53yZCwYFcDc6RzK06UYc482j3vCux2xbt2ubI/
CotsRAbN/u7RA5ofKDfjqGasuEtsJCvZ6pZgWvC1sSShOUanqcqJulLRK8ByngHfUHtk
iCKg==
ARC-Authentication-Results: i=1; mx.google.com;
spf=pass (google.com: domain of admin1@angel.ocn.ne.jp designates 153.149.233.14 as permitted sender) smtp.mailfrom=admin1@angel.ocn.ne.jp
Return-Path: <admin1@angel.ocn.ne.jp>
Received: from mbkd0213.ocn.ad.jp (mbkd0213.ocn.ad.jp. [153.149.233.14])
by mx.google.com with ESMTP id 81-v6si15855928pfw.261.2018.09.01.16.10.32;
Sat, 01 Sep 2018 16:10:47 -0700 (PDT)
Received-SPF: pass (google.com: domain of admin1@angel.ocn.ne.jp designates 153.149.233.14 as permitted sender) client-ip=153.149.233.14;
Authentication-Results: mx.google.com;
spf=pass (google.com: domain of admin1@angel.ocn.ne.jp designates 153.149.233.14 as permitted sender) smtp.mailfrom=admin1@angel.ocn.ne.jp
Received: from mf-smf-unw008c1 (mf-smf-unw008c1.ocn.ad.jp [153.138.219.102])
by mbkd0213.ocn.ad.jp (Postfix) with ESMTP id 44E042005B0;
Sun, 2 Sep 2018 08:10:28 +0900 (JST)
Received: from msgw008-03.ocn.ad.jp ([180.37.203.154])
by mf-smf-unw008c1 with ESMTP
id wF2CfsSribXPgwF2CfG9li; Sun, 02 Sep 2018 08:10:28 +0900
Received: from User (p1186067-ipngn200712niho.hiroshima.ocn.ne.jp [114.151.158.67])
by msgw008-03.ocn.ad.jp (Postfix) with SMTP id 42B83C59D61;
Sun, 2 Sep 2018 08:09:52 +0900 (JST)
Reply-To: <jeff44105@gmail.com>
From: "BANK OF AMERICA"<admin1@angel.ocn.ne.jp>
Subject: MESSAGE FROM BANK OF AMERICA
Date: Sun, 2 Sep 2018 01:10:29 +0200
MIME-Version: 1.0
Content-Type: text/plain;
charset="Windows-1251"
Content-Transfer-Encoding: 7bit
X-Priority: 3
X-MSMail-Priority: Normal
X-Mailer: Microsoft Outlook Express 6.00.2600.0000
X-MimeOLE: Produced By Microsoft MimeOLE V6.00.2600.0000
Message-Id: <20180901230953.42B83C59D61@msgw008-03.ocn.ad.jp>
To: undisclosed-recipients:;Notice that the real sender was from Japan: p1186067-ipngn200712niho.hiroshima.ocn.ne.jp. This is clearly not from Bank of America in New York.
While reading a e-mail text will not infect your computer, embedded images and especially attachments can. Good e-mail clients will block images in e-mails until you approve them. Never open an attachment unless you follow the above steps to verify that the sender is legitimate.
To show you the difference, here is a legitimate e-mail from me so you can see the difference in the header:
Return-Path: <jamesrome@gmail.com>
Delivered-To: webmaster@orcma.org
Received: from just174.justhost.com
by just174.justhost.com with LMTP id kEaPKwUTnVtWbwAArTHMMg
for <webmaster@orcma.org>; Sat, 15 Sep 2018 08:11:17 -0600
Return-path: <jamesrome@gmail.com>
Envelope-to: webmaster@orcma.org
Delivery-date: Sat, 15 Sep 2018 08:11:17 -0600
Received: from mx76.antispamcloud.com ([46.165.232.196]:50042)
by just174.justhost.com with esmtps (TLSv1.2:ECDHE-RSA-AES256-GCM-SHA384:256)
(Exim 4.91)
(envelope-from <jamesrome@gmail.com>)
id 1g1BI5-0007Me-7w
for webmaster@orcma.org; Sat, 15 Sep 2018 08:11:17 -0600
Received: from mail-yb1-xb29.google.com ([2607:f8b0:4864:20::b29])
by mx76.antispamcloud.com with esmtps (TLSv1.2:ECDHE-RSA-AES128-GCM-SHA256:128)
(Exim 4.89)
(envelope-from <jamesrome@gmail.com>)
id 1g1BHt-0002M6-4O
for webmaster@orcma.org; Sat, 15 Sep 2018 16:11:05 +0200
Received: by mail-yb1-xb29.google.com with SMTP id k5-v6so5973773ybo.10
for <webmaster@orcma.org>; Sat, 15 Sep 2018 07:10:53 -0700 (PDT)
DKIM-Signature: v=1; a=rsa-sha256; c=relaxed/relaxed;
d=gmail.com; s=20161025;
h=to:from:subject:message-id:date:user-agent:mime-version
:content-transfer-encoding:content-language;
bh=55XWXD9NPxm+omfraVCH6GQ2qOp+Xd1x54JB1lD5JhI=;
b=ioR/BBEiYtvjNhJcLYFHtp+pycN9+TKkMoTNYukkoQMWm0K12SP4bjXZ6HesMkrtw6
GsnmlXrLjvz1SnPIUsYkASa49ZlSpLl7z+QZ/Ldu4H36Hwy2NGO4EzM1akPggx20guxl
yihKqYRC6atLHoPU9u1MqIDUH/iaAMyt7RSDBlCnC8neiaHt1d01QyUcd7o7KqUgrNpC
JR0loA+F0caiQD4CeEzrkDw3SJXIc9lqd7U9ggcMotAtw4n2S2E9vKYXdKstDLgehzm5
tClzQWyNQ9iypQzLdsQ+O1GEpp6PEQ5nB5drscED5GAMqdim781oVHy3iXrg4vwCn14s
sSZw==
X-Google-DKIM-Signature: v=1; a=rsa-sha256; c=relaxed/relaxed;
d=1e100.net; s=20161025;
h=x-gm-message-state:to:from:subject:message-id:date:user-agent
:mime-version:content-transfer-encoding:content-language;
bh=55XWXD9NPxm+omfraVCH6GQ2qOp+Xd1x54JB1lD5JhI=;
b=oAZ8K8psyhSuNKHkW+kNQIAOnA9Y+Q6ew/xsg3jkXeJvox+DXHOODGz6damZAAAh90
T69u8Bw0SiDuH6YWhlvRAcFf+CTsM7sjaj9IIsehtvvYhR0uYG84b13unyvgUzneRuzM
nsqPZiAe86CaAamQ2/oA+1tWXQBn0fIHVoPam9OYADX5l0EHwE/h4VITU8+XtmG2hYbC
6koyFSYbvj/Dct6qB/90L4s1Uy5uRJ3JGJNOLFOhlr8cbE4YwloKghVcggPN0q3Y3cPg
m+gRx4lJI13F32t0QvM6m1pjbJnE4sfPMQBU452klT2v1KXg5fggtNe2nYOmvaPEdU7r
nNsg==
X-Gm-Message-State: APzg51DRQXBu1kZmfKiLNGdb5gjnzpPyb6dlwtANv2zZsxBhEEg/xYvW
Modoft2TQiwpiTbyQi9PHr2Zh0uA
X-Google-Smtp-Source: ANB0VdZ4YojFZbWTwWzBxm9Uuw3wijVl0a965Mhid4ztbMrBLuOwNbbpJp+19XWqOJ7/EiYI4W5YBg==
X-Received: by 2002:a25:cbc8:: with SMTP id b191-v6mr7519987ybg.223.1537020651508;
Sat, 15 Sep 2018 07:10:51 -0700 (PDT)
Received: from JARMAC.local (c-73-121-14-196.hsd1.tn.comcast.net. [73.121.14.196])
by smtp.gmail.com with ESMTPSA id s63-v6sm5566520ywd.63.2018.09.15.07.10.50
for <webmaster@orcma.org>
(version=TLS1_2 cipher=ECDHE-RSA-AES128-GCM-SHA256 bits=128/128);
Sat, 15 Sep 2018 07:10:51 -0700 (PDT)
To: webmaster@orcma.org
From: James Rome <jamesrome@gmail.com>
Subject: This is a test
Message-ID: <366df68d-0466-8f50-2ffb-5dd94329886c@gmail.com>
Date: Sat, 15 Sep 2018 10:10:50 -0400
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.13; rv:60.0)
Gecko/20100101 Thunderbird/60.0
MIME-Version: 1.0
Content-Type: text/plain; charset=utf-8; format=flowed
Content-Transfer-Encoding: 7bit
Content-Language: en-US
Received-SPF: pass (mx76.antispamcloud.com: domain of gmail.com designates 2607:f8b0:4864:20::b29 as permitted sender) client-ip=2607:f8b0:4864:20::b29; envelope-from=jamesrome@gmail.com; helo=mail-yb1-xb29.google.com;
X-SPF-Result: mx76.antispamcloud.com: domain of gmail.com designates 2607:f8b0:4864:20::b29 as permitted sender
Authentication-Results: mx76.antispamcloud.com; dmarc=pass header.from=gmail.com
Authentication-Results: antispamcloud.com; spf=pass smtp.mailfrom=jamesrome@gmail.com; dkim=pass header.i=gmail.com
X-AntiSpamCloud-Class: whitelisted
X-AntiSpamCloud-Evidence: sender
X-Recommended-Action: accept
X-Filter-ID: EX5BVjFpneJeBchSMxfU5k4vttopaznJi+Oy9Zlg/zMoS0oCIPR/rZSAJyoppnqc4iF/GF/s/jIX
rGukyuoBNXDl5xqzAR3iXAUhHqRFFAvGkupNenPrxEEkt+tCfY2t9YrRV4WvzFt2037yKVsLxkyR
hh+lk+itmHMUtkInh7Tq32fObvm4BUqXBDU2nHdDl1R7/ClUcVcJ4Qk8yjrl1iTg127TqHZDxA/k
ZB41Rh//I6dVM9aCE3XwJtDzHS3TXLCgQeVFXJbShRwKWlqpy+42Vki7412dpbhrD2d47zYqyS7y
viWX4Y+TSSXoHLdLbweT2+CRGv/wRpjFRRmp/QCB2MaZkZ2VaougMWpoIHvcwaxVtBcR0F+RGqyP
zltVayJlvHoXTBhS4eFwr87chpjNZXvY/LaOLYt/eqQRpiYILb/DK32fbx7z0dUW4eBs0on3OmSH
gIFVk16+U330sDbf7Pr0wN7IAExZRosm0MLbYXv5WOsQcB/yA02SEVSGIrv3F28sfojuZI3S+Bdc
3lnsyWu8Q0HDoORE+fy5gr3LgKffTIgl7nuGO/IJU1342OUMeHyTpNN0eXybX/w7/6hAkYmm8VLk
ulb8pHdV1ZM5HoPL7XZG1wG2jCHBGpvBGplHcpVCCoX989hgB8R+yNMcQs06Siyku1OXfA2p6TjD
PfbvFi2v+4eN23Y33UiTKLILAej3Udqot7L/rL7e+zWI7l3aGHQGuJm+qKiMbmpgrlzScZ9BKehd
zB4Xx60LiD9/tuWoAGBqY4cqG4XYbrV4D5juttJ+Ne5zs2e7CtOIWGrMph8g/xbYmARR4eVvV2G7
4uRzYVEz+iWN4lDeuZzgDCICWjJzsTlWpuDqBSeEgPjdq+SVnW0lHN3HIsIWK35OgCET3t6v6yUd
o2J+0tqA3xvMIqc3MGYVXxCnrJSIP3+25agAYGpjhyobhdhuEmgCmgCoXJeXpXuyrHo9XppQDpfP
mup33qUtmQ53RslWBb39uS1TjWG2Inx+Ts2Qvce5bLLLmf+d7Dm4btGCTQ==
X-Report-Abuse-To: spam@quarantine2.antispamcloud.com
X-Spam-Status: No, score=1.5
X-Spam-Score: 15
X-Spam-Bar: +
X-Ham-Report: Spam detection software, running on the system "just174.justhost.com",
has NOT identified this incoming email as spam. The original
message has been attached to this so you can view it or label
similar future email. If you have any questions, see
root\@localhost for details.
Content preview: Legitimate e-mail from me. -- James A. Rome 116 Claymore Lane
Oak Ridge, TN 37830-7674 865 482-5643 //jamesrome.net [...]
Content analysis details: (1.5 points, 5.0 required)
pts rule name description
---- ---------------------- --------------------------------------------------
0.0 URIBL_BLOCKED ADMINISTRATOR NOTICE: The query to URIBL was blocked.
See
http://wiki.apache.org/spamassassin/DnsBlocklists#dnsbl-block
for more information.
[URIs: jamesrome.net]
1.0 SPF_SOFTFAIL SPF: sender does not match SPF record (softfail)
0.5 FREEMAIL_FROM Sender email is commonly abused enduser mail provider
(jamesrome[at]gmail.com)
-0.1 DKIM_VALID_AU Message has a valid DKIM or DK signature from author's
domain
-0.1 DKIM_VALID Message has at least one valid DKIM or DK signature
0.1 DKIM_SIGNED Message has a DKIM or DK signature, not necessarily valid
0.1 AWL AWL: Adjusted score from AWL reputation of From: address
X-Spam-Flag: NO
Legitimate e-mail from me.
Notice that I have been authenticated by the sending organization, Gmail. It even has the name of my computer.
How to view headers on mobile devices
Apple Mail
- Open Apple Mail.
- Double-click to open the email message.
- Choose "View" at the top menu and select "Customize Toolbars."
- Drag the "Full Headers" or "Long Headers" icon into your toolbar and save changes. See Figure 1. Figure 1.
- Now, you can click on "Full Headers" or "Long Headers" to the top of the toolbar.
Gmail
You cannot view headers in the Gmail app (Android or IOS). You will have to use a browser to go to Gmail.com. Once there:
- From a browser, open Gmail.
- Open the email you want to check the headers for.
- Next to Reply
, click the Down arrow
.
- Click Show original.
The headers will show in a new window, including fields like authentication results. To get the full message header, copy everything below "Download original."
Examples of malicious e-mails
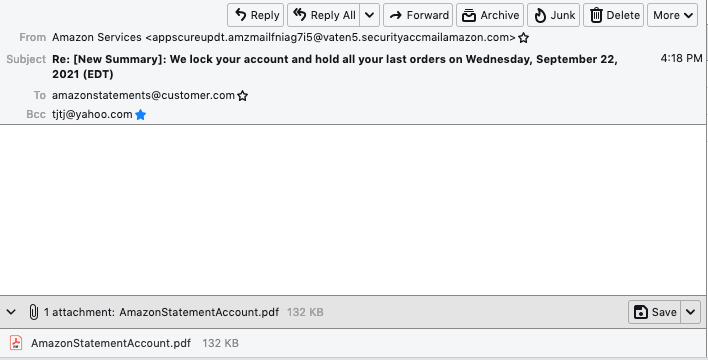
Notice that the from address is not amazon.com, and the subject is in poor English
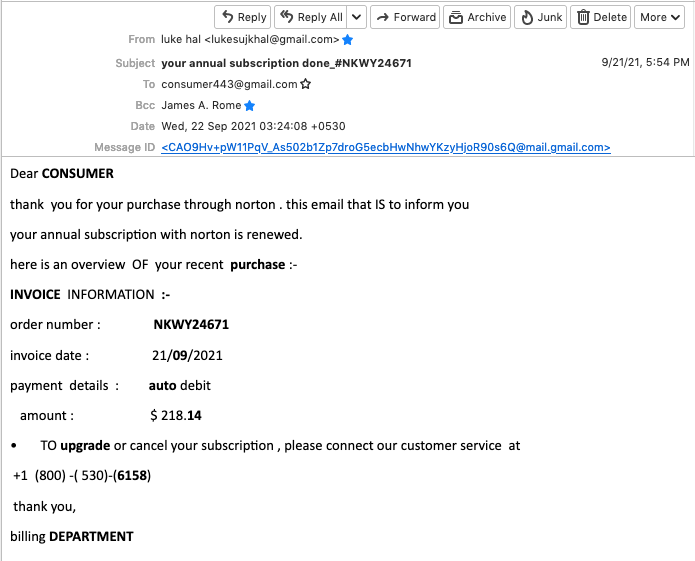
This would be scary if you actually have a Norton account. The from address seems legitimate (I examined the full header), but it is not from Norton or a recognized software agent (such as Cleverbridge). I did not call the 800 number. If these is a charge, you can dispute it on your credit card statement. By the way, always use a Credit (not a Debit) card! Credit cards also absolve you of liability for fraudulent charges. Debit cards remove the money from your account while it is disputed. And I get a 2% rebate on my credit card purchases. And who is consumer443@gmail.com??

Definitely do not open the attached invoice! Files with XLSM extension is a type of Spreadsheet files that support Macros. Macros can do almost anything on your computer.
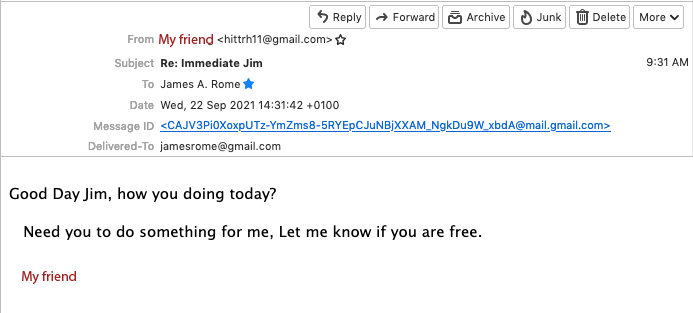
These emails are very common, and they always end up asking you to send money, buy gift cards, etc. Note that the e-mail address is not that of my friend. When in doubt, call your friend.
This is an example of a highly-targeted e-mail called spear phishing. It knows my hosting provider, and if I click on any link, it perfectly reproduces the A2hosting.com login page (but look at its URL!):

Phone Phishing
We all get many spam phone calls asking us to buy auto insurance, medical equipment, and so forth. Or warning you that your social security number is involved in fraud, or that your Amazon order for a lot of money has issues.
This is in spite on my having Nomorobo on my land and cell lines, and assurances from Xfinity and T-Mobile that they block spam calls. Ha Ha.
Here are some things to know:
- The government will never call you on the phone without writing first.
- Most phishing calls come from your area code. Isn't it amazing that Amazon has a local office with the caller ID GR Baker? These calls are almost always spam.
- Comcast claims that [V] before the caller ID means the caller is verified, but they just add that to their spoofed Caller ID.
- I am getting calls supposedly coming from my local hospital trying to sell me medical alert devices and subscriptions.
- If you try to call the number back (a good strategy with a persistent caller -- "I will call you back") It is almost always disconnected. Why don't phone companies block phone calls from disconnected numbers?